NIST 800-171 Critical Controls
Understanding NIST 800-171 Critical Controls is important if your company stores Controlled Unclassified Information (CUI), and you are the prime, subcontractor, or a 3rd party cloud provider. The following information will help you understand the critical areas that require special attention.
Contractors are encouraged to implement adequate safeguarding standards in NIST 800-171 as soon as practical since the deadline for compliance has elapsed.
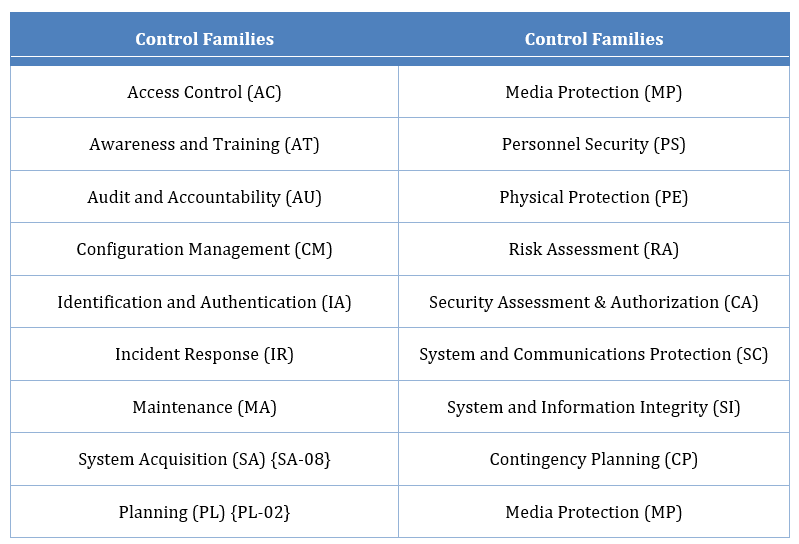
There are 110 separate controls that fall into the following 14 families:
While all these controls are important, a few stand out due to their complexity or difficulty of implementation, and so deserve further scrutiny.
Configuration Management (CM)
A secure baseline is crucial not just for compliance to NIST 800-171, but for general security hygiene purposes as well. Configuration management entails managing baselines for systems. With larger enterprises and more complex systems this can be quite difficult, and detailed change management processes should be followed.
A full system inventory helps organizations create configuration items (CI), which are managed by the change configuration program. CI’s represent the baseline configuration for hardware, firmware, and software, and are defined as an aggregation of these, leading to the production of a manageable baseline.
Because organizations are required to have a change control program (CCP) they will need a formal change control board, which is made up of the leading IT professionals in each relevant department. Any change to the infrastructure, be it a patch, upgrade, or change to the environment, must be analyzed and approved by the board. A security impact analysis must be conducted for each change and signed off on by security personnel. When a change is approved, updates to the configuration items can be made.
Each CI must meet certain benchmarks that meet mandatory configuration settings that are hardened to be as restrictive as possible. The following are examples of hardening benchmarks: DISA Security Technical Implementation Guide (STIGS), Center for Internet Security (CIS) benchmarks, SANS, and vendor specific guides. The server hardening project takes time to complete due to testing, roll backs, and getting concurrence from system owners to do the work. DOD Contractors will need to budget and plan for hardening of infrastructure platforms such as firewalls, databases, operating systems, and applications.
Audit & Accountability
This is another requirement that could be difficult to achieve but will pay security dividends in the future. Audit logs need to be collected from infrastructure platforms such as servers, routers, switches, databases, VPN, intrusion prevention systems, and firewalls. DFARS 252.204.7012 requires contractors to notify DOD of data breaches within 72 hours. Furthermore, the evidence must be saved for 90 days for forensic investigations.
Security Information and Event Management (SIEM) tools, are necessary to capture pertinent security, operational, and auditing events in an organized manner. This aggregation of event information increases efficiency of administrators and makes the auditing process less painful and more reliable. A multitude of SIEM tools are available such as LogRhythm, Splunk, Alien Vault, and SolarWinds. Contractors need to budget for the implementation and maintenance of these appliances.
Identification and Authentication
Thankfully, the world is finally coming around to multifactor authentication. Thanks to technological advances such as hardware tokens, software tokens, and mobile phones, this has become less difficult to implement.
Contractors should note that DFARS 252.204.7012 has a requirement to implement two-factor authentication for Local and Network Access for privileged accounts. Non-privileged (ordinary) users require two-factor authentication for Network Access Only. Some vendor solutions are not able to fulfil this unique requirement. Contractors are urged to compare products that provide authentication capabilities from the onset of users logging on to the network.
Additionally, this control family covers password policies, which are critical, as many small businesses tend to have weak password policies.
Other Control Families
Other interesting control families such as Incident Response, Security Assessments, and Personnel Awareness and Training, will provide added value if not already implemented. Implementing these safeguards will enhance the security posture of organizations.