We Empower Brilliant Minds to Achieve Great Things
CKSS and The CMMC Lifecycle
CKSS is deeply involved in every aspect of the Cybersecurity Maturity Model Certification (CMMC) Lifecycle including remediation and assessments. CKSS supports Organizations Seeking Certification (OSC) by offering consulting and audit preparation.
Our team of cybersecurity experts brings over 75 years of combined experience to enhance cybersecurity programs:
- Remediation
- Assessing
- Interpreting standards, guidelines, and best practices
This wealth of knowledge ensures that you have a skilled and versatile team supporting your CMMC journey, making CKSS the ideal choice for your CMMC Compliance needs. For more details, review our CMMC blogs to learn more about the CMMC topics.

Demystify DFARS/CMMC Regulations
We Make Cybersecurity Simpler
CKSS simplifies cybersecurity by understanding and eliminating the complexity and costs that can make it challenging. We provide the most comprehensive suite of integrated security services in the market, utilizing the best available technologies.
How CKSS Accelerates CMMC Compliance
Trusted Partner
We have demonstrated a track record of aiding our customers with common security technology solutions and frameworks: NIST SP 800-53, NIST SP 171/CMMC, HIPAA, ISO 27001, SOC2, GDPR, PCI-DSS, & HIPAA




CMMC Frequently Asked Questions
The Cybersecurity Maturity Model Certification (CMMC) is one of the most significant compliance requirements facing Department of Defense contractors today. With certification tied directly to contract eligibility, organizations handling Controlled Unclassified Information (CUI) must understand not only what CMMC requires, but how to implement it correctly, document it properly, and sustain it over time.
This FAQ page is designed to answer the most common and critical questions we hear from small and mid-sized defense contractors preparing for CMMC Level 2. From cost expectations and timelines to readiness, enclaves, assessments, and ongoing compliance responsibilities, these answers reflect real-world assessment experience, not theory.
At CKSecurity Solutions (CKSS), we focus on practical, hands-on CMMC readiness. That means helping organizations close gaps, align documentation with actual operations, define clear system boundaries, and prepare defensible evidence that stands up to third-party assessment. Whether you are just starting with a gap assessment or preparing for a C3PAO audit, these FAQs will help you make informed decisions, avoid common pitfalls, and reduce risk throughout your CMMC journey.
If you have additional questions or need support tailored to your environment, CKSS is here to help.
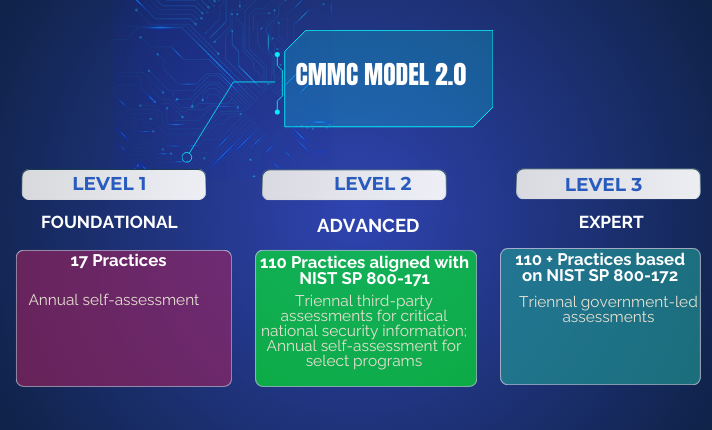
Does Your CMMC Framework Level Up?
The CMMC levels are commensurate with the type and sensitivity of information to be protected. As a result, the CMMC levels are categorized as follows:
The Evolution to CMMC 2.0
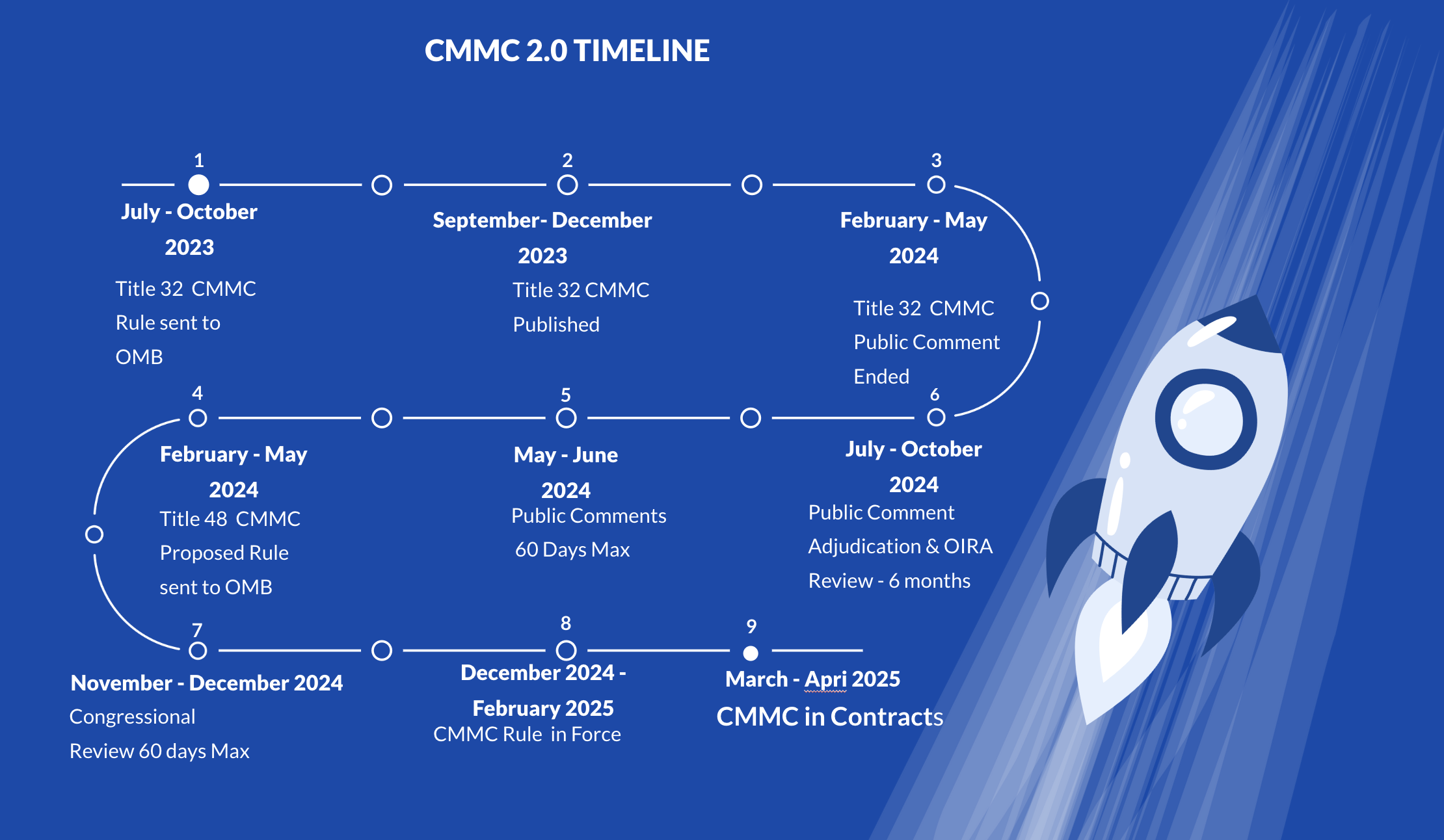
CMMC 2.0 Timeline
CMMC 2.0 is in the final phase of rulemaking and is expected to take effect by late 2024. Beginning in 2025, the DoD will gradually roll out CMMC requirements across its programs over a five-year period, eventually making CMMC compliance mandatory for all programs.
Expedite Risk Mitigation With DFARS/CMMC Compliance Templates
Combine your one-on-one consultative work with a ready to go CMMC Full Compliance Toolkit. Over 300 pages of security policies, procedures, resource plans, security plans, checklists, and bonus documents.

Cybersecurity Resources
- Whitepapers
- Articles
- Blogs
Accelerate Compliance Whitepaper
Repercussions of Biden’s Executive Order on Improving the Nation’s Cybersecurity for Federal Contractors
CMMC NIST Policy Templates: What Are The Benefits?
Trusted Memberships & Affiliations